A new Google study has pushed the Bitcoin quantum vulnerability debate back into the spotlight. Researchers say future cryptographically relevant quantum computers may be able to break the elliptic curve cryptography that helps secure Bitcoin and other digital assets with fewer resources than previously estimated. While this is not an immediate threat today, it is a serious long-term security issue that the crypto industry can no longer afford to ignore.
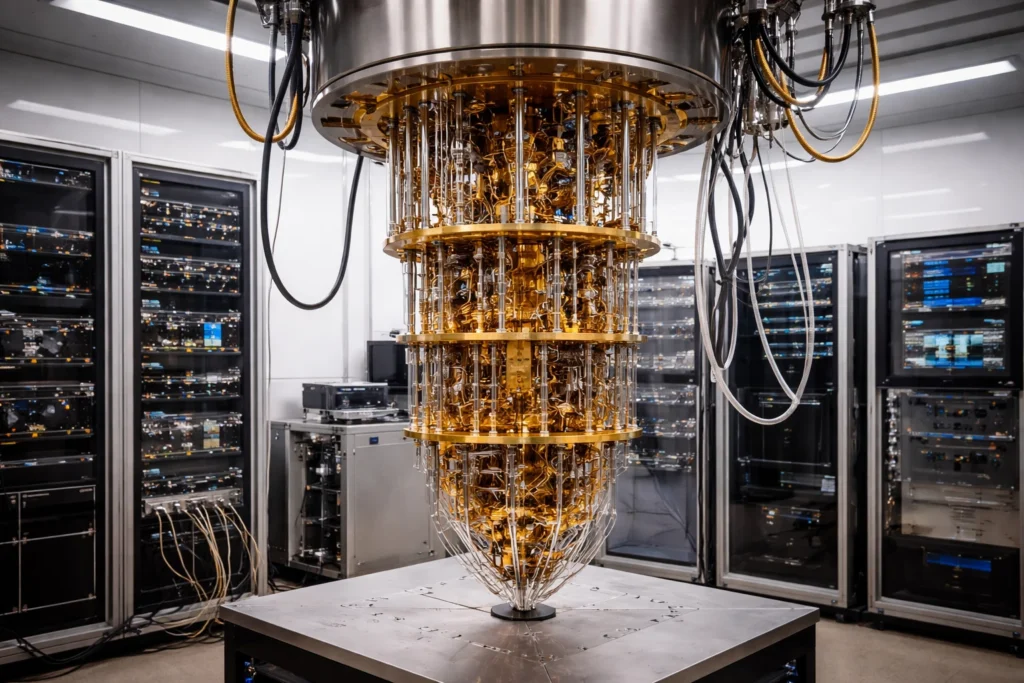
According to Google Quantum AI’s whitepaper, Shor’s algorithm could solve the 256-bit elliptic curve discrete logarithm problem used by modern blockchain systems on certain future “fast-clock” quantum architectures in minutes, using fewer than half a million physical qubits. The paper also distinguishes between faster and slower quantum hardware models, arguing that the first practical attacks may depend heavily on the type of machine that arrives first.
That matters because the Bitcoin quantum vulnerability is not just a theoretical headline. In the paper, Google discusses how a future attacker could potentially derive a private key from an exposed public key quickly enough to target some public mempool transactions. In practical terms, that means some Bitcoin transactions could become vulnerable during the window between broadcast and confirmation if powerful enough quantum systems ever become available.
Still, there is an important nuance here. Google is not saying Bitcoin can be broken today. The hardware required for this kind of attack does not currently exist at the necessary scale and fault tolerance. What the study changes is the risk calculation. It suggests that the resources needed for a future attack may be lower than many people assumed, which narrows the margin for error for developers, exchanges, wallet providers, and blockchain communities.
The biggest concern is that the Bitcoin quantum vulnerability could affect more than just one coin or one blockchain. Any system that still depends on vulnerable public-key cryptography may eventually need to migrate. Google’s paper expands the discussion beyond Bitcoin and points to wider risks for other cryptocurrencies, digital assets, and blockchain-based financial systems. It also highlights broader concerns around dormant wallets, exposed keys, and advanced blockchain features that may enlarge the attack surface over time.
So what is the solution? The answer is post-quantum cryptography, often called PQC. Google has publicly said it is working toward a 2029 migration timeline for quantum-safe cryptography across its ecosystem, and NIST has already finalized its first principal PQC standards. That does not mean every crypto platform can simply flip a switch overnight. Migration is likely to be complex, slow, and politically difficult in decentralized ecosystems, which is exactly why many experts argue that planning needs to begin long before the first truly dangerous quantum machine appears.
For Bitcoin, the challenge is as much social as technical. Any meaningful transition would likely require wallet upgrades, address hygiene, developer coordination, exchange support, and broad community agreement. The longer that preparation is delayed, the harder it becomes to respond calmly later. A late migration could create confusion, split ecosystems, or leave older funds and abandoned wallets especially exposed.
The good news is that the Bitcoin quantum vulnerability is still a preventable problem, not an active collapse scenario. The crypto industry has time to prepare, but not unlimited time. Google’s study is best understood as a warning shot: quantum risk is moving from distant theory toward realistic planning. For Bitcoin and the wider blockchain world, post-quantum readiness is no longer optional future-proofing. It is becoming a core security priority.




